Introduction
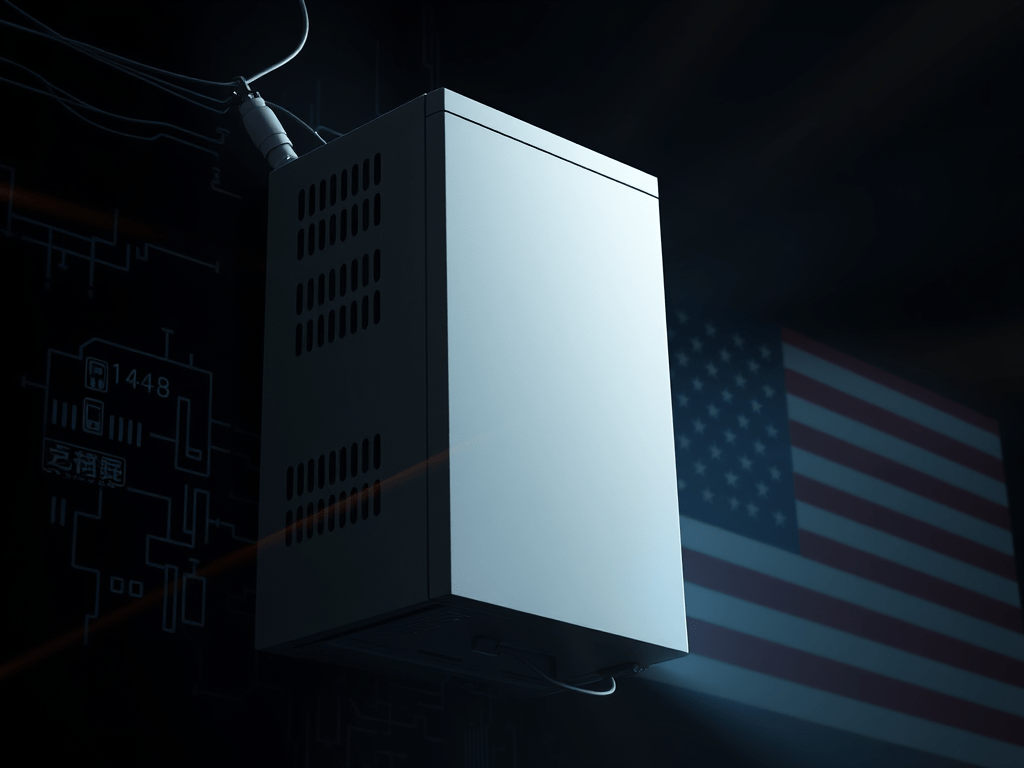
A new cybersecurity alert has emerged from the United States, focused on potential threats embedded in foreign-manufactured solar power infrastructure. Former National Security Agency (NSA) analyst Rocky Cole has sounded the alarm on rogue communication devices embedded in Chinese solar inverters, raising serious concerns about the national security implications of foreign-made technology in America’s critical infrastructure.
China’s Rogue Devices and U.S. Concerns
According to Cole, several Chinese-manufactured solar inverters have been found to contain undocumented communication channels, enabling remote access that could be exploited during a geopolitical crisis, particularly in the event of a conflict with Taiwan. Over the past nine months, multiple suppliers have been flagged for using such compromised devices.
These devices, if left unchecked, pose a risk of massive disruption to U.S. commerce, especially in a world increasingly dependent on clean energy and digital control systems.
Key Developments in the China-U.S. Solar Cybersecurity Case
| Aspect | Details |
|---|---|
| Rogue Devices | Found in Chinese solar inverters with hidden communication channels. |
| National Security Threat | Devices could allow remote access to U.S. infrastructure. |
| Legal Mandate in China | Chinese law requires companies to cooperate with state intelligence agencies. |
| Potential for Cyberattacks | Devices may be activated during geopolitical tensions (e.g., Taiwan conflict). |
| Supply Chain Risks | Rogue components have been found in multiple suppliers in the last 9 months. |
| Call for Oversight | Urged for strict supply chain vetting to eliminate backdoors in imported technologies. |
| China’s Response | Chinese embassy refutes allegations; claims tech exports are for development, not spying. |
Beyond China: Other Notable Cybersecurity Threats
China is not alone in this space. Multiple countries have demonstrated state-sponsored cyber aggression, often targeting the U.S. or its allies. Below is a summary of key global cybersecurity threats:
| Country | Threat Activities |
|---|---|
| Russia | Election interference (2016), ransomware attacks (e.g., Colonial Pipeline), Fancy Bear group espionage. |
| Iran | Cyberattacks on financial institutions and energy infrastructure; use of proxy hacker groups. |
| North Korea | Responsible for WannaCry ransomware; known for financially motivated cyber crimes. |
| Turkey | Targets journalists, dissidents, and adversaries in regional disputes via cyber ops. |
| Venezuela | State-affiliated hackers targeting internal opposition and collaborating with allies for cyber expertise. |
| Non-State Actors | Groups like Anonymous, Lizard Squad, etc., exploit vulnerabilities for ideology or profit. |
Implications for U.S. Policy
These developments call for an urgent policy response:
- Stricter Import Scrutiny: The U.S. may need to limit or ban hardware imports from nations with weak cybersecurity transparency or hostile intent.
- Strengthened Cyber Oversight: Enforce traceability and inspection protocols across energy and digital infrastructure.
- Strategic Tech Independence: Accelerate domestic production of critical components like solar inverters to reduce foreign reliance.
- International Cooperation: Collaborate with allies to share threat intelligence and jointly respond to malicious cyber actions.
Conclusion
The emerging revelations about China’s solar inverters are not isolated. They are part of a broader global pattern where cyber threats have become a strategic tool for espionage, sabotage, and coercion. As the U.S. energy grid and economy become more interconnected, securing the supply chain of critical hardware—from solar inverters to cloud infrastructure—is not just a technology issue but a national security imperative.





Leave a comment